Introduction
Hackers, crackers, pirates: The media and the general public have unfortunately seized on these terms for a good couple of decades. Words, like a speech, keyboards and knives are all powerful tools for both good and evil ends.
Nowadays, with the development and acceleration of means of communication, the goalposts in the information game have moved: it’s no longer a matter of getting a scoop on the most pertinent information or producing the most tightly evidence-based file. No, today the goal is to make the biggest “buzz†and to do it fast: the winner is the one who publishes information as quickly as possible, even if this means skipping the hard slog behind true journalism.
Quality no longer counts, speed is all that matters. This trend first emerged several decades ago, and is now accelerating daily, leading in turn to producing “fake newsâ€, shortcuts and approximations even faster. I will certainly be covering this broader topic in more detail in a later post, but for now it is serving merely as an introduction to a topic that’s close to my heart: the abusive, indiscriminate use of the term “hacker†to refer to all sorts of stuff.
The back-story: who are hackers?
Rather than launch into an incredibly long-winded explanation, I’ll start by telling you what they are not: pirates. That’s not a typo: hackers are not pirates.
Let’s kill off this urban legend once and for all. Despite what pirates themselves would have you believe when calling themselves “hackersâ€, no, there are no white-hat, black-hat or even grey-hat hackers. No, there’s no such thing as an “ethical hacker†just as there’s no such thing as an “unethical hackerâ€. For a true hacker, ethics are not optional; it’s what dictates every single thing they do.
I know, you’re going to tell me that even “reputed professionals†(who more often than not in fact, are “well-known professionalsâ€, which is not exactly the same; I’ll discuss this at more length in another post) use the term “hacker†nowadays to designate pirates. For years you have been reading this same definition in the press, a press which doesn’t often know what they are talking about. On this topic, how many “worms†have been wrongly called a “computer virus†in the press or by “experts†invited to a BFM TV studio?
This is far from reflecting reality, very far from what you often read or hear on the subject, whether in the media or, even worse, at so-called professional conferences on the subject.
So I’ll put it as clearly as possible: no, hackers are not pirates, and so no, they *never illegally hack* into an information system that doesn’t belong to them, whatever their motivations.
Take it from me: those who do that are crackers, I’ll discuss it in more detail below.
To sum up the definition of a hacker (at least in the field of IT and communication), is a matter of a few words only: a hacker is someone with a passion for how operating systems and networks work. While they are often software developers this is not a sine qua none.
Harnessing their advanced knowledge in various fields, they often discover new vulnerabilities at various levels (networks, systems, application etc.), however these discoveries *are not used against other systems*. A hacker obviously might happen upon vulnerability in a system that doesn’t belong to them, just as you can happen upon a problem in a bus or in a friend’s car.
To be able to assess the quality of a tree properly, you must not only gauge its appearance or fruit: you also need to look at its roots. To understand about hackers’ roots, we’re going to rewind a little way, back to when the term “hacker†first came on the scene: not so long ago for some, and eons for others!
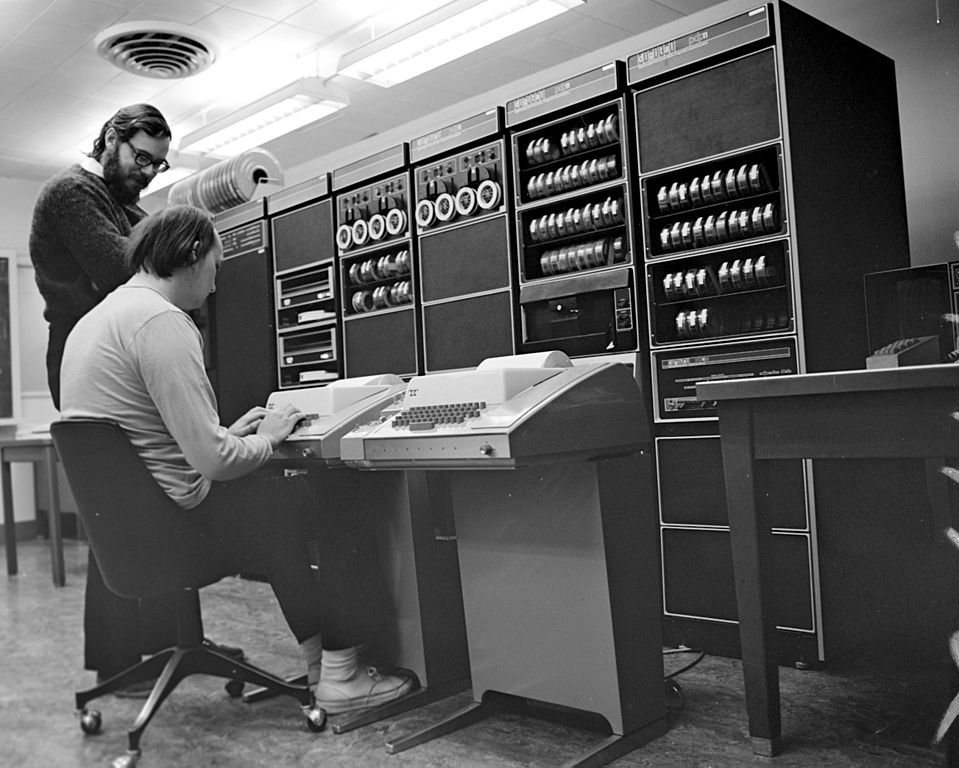
Ken Thompson and Dennis Ritchie at PDP-11
The story first started up back in the 1950s, at the famous MIT (Massachusetts Institute of Technology), when the first ever computers (huge cupboards that could take up an entire room) came into being. At night, the first hackers, mostly students with a bent for this new invention, spent their nights coding, debugging and experimenting on these machines, constantly improving how they operated.
These eager enthusiasts soon unwittingly morphed into a community, under the same banner, sharing more ethical than technological values: “all information must be freeâ€.
Hackers are not destructive, they are progressive: for example, the people who created the Internet and operating systems such as Unix and Linux may be considered to be hackers. Ken Thompson, Steve Wozniak, Dennis Ritchie and Richard Stallman are all hackers.
So, contrary to what you might read in so-called underground publications, in which hackers are described with a cigarette hanging from a corner of their mouth (when they’re not total stoners), with straggly hair and a beer can on their desk (the modern addition to the look being the hoodie), true hackers refuse on principle *any form of dependence and submission* for the very good reason that it would hamper their liberty and development.
Crackers (computer pirates)
All this raises the question: just who are these people the press go on about so often then? The ones stealing credit card numbers, usurping digital identities, creating viruses, and even worse putting the lives of millions in danger? They are computer pirates: or crackers, i.e. people who deliberately compromise the integrity of an information system, generally (although not always, there are exceptions) to malicious ends.
Crackers can destroy or steal data, attack other systems, cause all sorts of harm. They have various motives, and are not necessarily destructive. There are several categories and sub-categories of crackers (pirates). Many like to self-proclaim themselves as hackers, which then casts doubt in the minds of those who don’t know. Others prefer the term “white-hat hackerâ€: yet while cracker motives may vary depending on the situation (interest, challenge, revenge, money, contract, information) crackers remain pirates.
An infinite minority of pirates boast an excellent level, close to hackers (which they may have been previously) in terms of skill and passion. Some hackers become pirates: once they have crossed over (the mens rea, I’ll come back to that later), and for as long as they stay on that side, they are no longer hackers, they are crackers. Sometimes the crossover happens in the opposite direction with a talented pirate falling into the rank to become a hacker.
Ultimately, the difference between hackers and cracker is mens rea, i.e. a criminal mindset, or guilty intention. Mens rea is expressed in Latin thus: « Actus non facit reum nisi mens sit rea« , meaning that it’s not the committing of a crime that makes an individual a criminal but their mindset or intention of committing a crime.
Remember that the vast majority of pirates don’t have much to do with hackers: they are often low-skilled, making do with automatic operating tools (of which there are more and more and increasingly accessible nowadays) randomly searching for machines with potential vulnerabilities. Hackers and talented crackers alike often scornfully dub them “lamers†or “script kiddiesâ€.
The most dangerous and talented crackers have nothing to do with the clichéd “little IT genius†profile with autistic tendencies hiding behind their screen often depicted in TV series.
The weakest link in the “safety†chain of an information system remains above all the human factor, and, it’s often knowledge and exploitation of human weakness, via Social Engineering (the art of influencing and manipulating) which make the difference, rather than the possession of a few 0-day exploits (that is, exploiting a vulnerability as yet unpublished). Knowing the bare bones of psychology, knowing how to inspire immediate trust with a mere phone call or written message are now compulsory skills for a significant degree of success in penetrating closely guarded networks and information systems.
Lastly, it’s true that while an exception has never confirmed a rule, many rules do have exceptions: this is the case for those individuals who are always sitting on the fence, known as “grey-hatsâ€, who don’t exactly fit in either categories (pirate or hacker).
However we need to bear in mind that these exceptions have now been out of date for years. For insight into how these exceptions came about and even how they have been the source of this confusion, we have to come back to the very beginnings of Internet, when BBS and parallel networks like GTI were at their peak, when working on a UNIX system was unthinkable for enthusiasts. This operating system was reserved for wealthy organisations that could treat themselves to THE machine and UNIX with it. Even if you saved up for over a year, the man in the street, however enthusiastic, could not seriously imagine acquiring such systems and thus learn how they worked. At the time some hackers managed to penetrate certain IT systems, not to steal data or do any harm but simply to be able to study the system and learn more about its possibilities and limits.
And, while this motivation was perfectly understandable, that time is past: with the arrival of Gnu/Linux and other free systems, and now the generalisation of virtualisation, anyone can either retrieve some old machines in a skip or for a derisory sum, and set up their own lab: networks, systems, routers and servers to study the cogs down to the last detail, or use one of many free virtualisation solutions available to set up their own “virtual security laboratoryâ€.
I could say much more, probably enough to fill a book or several, but I hope this post will contribute to setting the record straight, at least in the eyes of some, on the true state of this exciting world in which unfortunately, as in many other fields, conventional wisdom and prejudice have long prevailed over the media image of true hackers.
Christophe Casalegno
You can follow me on : Twitter | Facebook | Linkedin | Telegram | Youtube
Laisser un commentaire